No audio available for this content.
Achieving PNT resilience for critical infrastructure applications
GNSS are magic. They are. One dictionary defines magic as “a power that allows people (such as witches and wizards) to do impossible things by saying special words or performing special actions.” By this definition, we have all become witches and wizards, doing what previous generations would have deemed impossible.
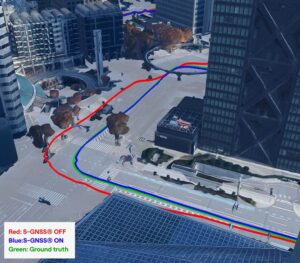
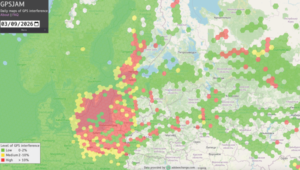
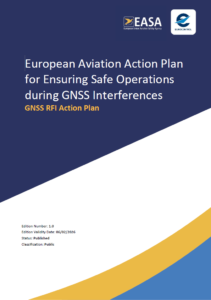
This magic, however, can be affected by external forces that render it useless at best and, at worst, dangerous. Warnings about GNSS positioning, navigation and timing (PNT) service vulnerabilities have been raised for 25+ years. Numerous organizations have warned of the potential safety, security and economic impacts of GNSS interference. Still, like modern-day Cassandras, their warnings have been ignored, and sole use of PNT services that rely on space-based signals continues to expand.
“Magic services” are addictive and cannot be ignored. Yet, it is well past the time to merely admire the problem of GNSS interference — benefitting from magical GNSS services while ignoring existing and emerging threats and challenges. It is time to draw a line and implement resilient, complementary PNT solutions to support all critical infrastructure sectors and applications in the event of any GNSS disruption, due to jamming or spoofing or systemic causes. “Magic” is magical when it works. When it does not, first and foremost, it should “do no harm.”
Threats, Challenges and Needs
Presidential Policy Directive (PPD) 21, Critical Infrastructure Security and Resilience, issued in 2013, defines resilience as “the ability to prepare for and adapt to changing conditions and withstand and recover rapidly from disruptions.” It also notes that “resilience includes the ability to withstand and recover from deliberate attacks, accidents, or naturally occurring threats or incidents.”
In 2016, the UK Department of International Development noted that “Resilience covers both ‘physical and societal systems” through four “R” principles: robustness, redundancy, resourcefulness and rapidity (see Figure 1).

More recently, Andy Proctor (RethinkPNT) pointed out that “A resilient PNT system protects its critical capabilities (assets) from harm by using protective resilience techniques to passively resist or actively detect threats, respond to them, and recover from the harm they cause.”
Policies, processes, financial arrangements and incentives are also crucial to achieving resilience — and that has been, and remains, the problem. Lacking the emergence of strong leadership from our institutions, the ability to achieve actual resilience will continue to falter and admiration of the problem will continue.
Developing a resilient PNT system is always a balance of technical complexity and non-technical aspects, for example, costs. The key consideration for users must be the required performance metrics they need for their use-case(s) to ensure their resilience — including accuracy, availability, integrity, continuity and coverage. The one least understood and many times omitted is integrity — the level of trust a user/use-case needs to safely and securely use the PNT services. The ability to trust PNT services must always be a consideration for critical infrastructure applications.
Unfortunately, many users of critical infrastructure PNT do not know some of the PNT metrics they need to ensure safety and security. More troubling, there is no guidance as to what constitutes “significant economic impact” (see PPD 21) or acceptable economic loss — and over what period or range of use cases. This understanding will require analysis of their design, development and operational experiences, and working with PNT systems engineers to first derive these metrics and then drive the continuous improvements (see Figure 2) needed to achieve and retain truly complementary PNT capabilities. Without clear metrics and guidance, one cannot claim that any solution will meet any “required level of resilience.”

Supporting PNT Users
As with all systems engineering (SE) activities, PNT system resilience begins with identifying and documenting user needs based on their specific user stories/use cases. Figure 3 depicts different aspects of resilience that can be sought, depending on the unique use-case “demands.”
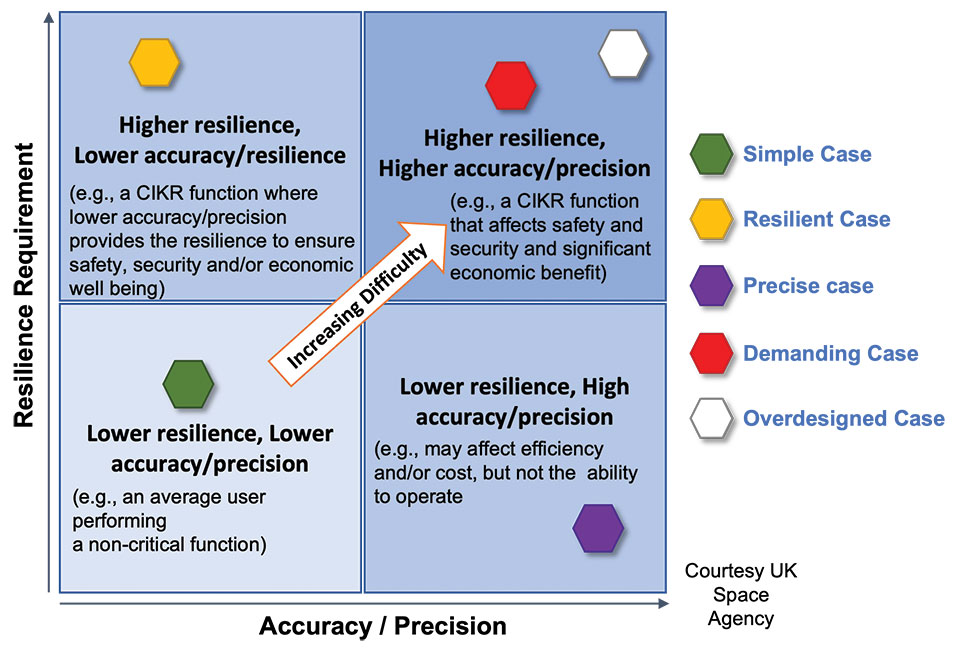
While the resilience needs of different use cases will differ, for any specific use case, a given “PNT solution” will either achieve the required/threshold level of resilience (based on the operational environment) or it will not. Some use cases may also require fail-safe or fail-soft capability and the ability to recover to known, trusted and usable states. Shouldn’t many, if not all critical sector use cases require this?
Equally important is the identification of risks and threats, as they are critical to understanding the challenges that the system must face while continuing to provide the necessary P, N and/or T service performance. It is also key to understand and document the system architecture and environment in which it must perform. With knowledge of a user’s needs, the threats, hazards and challenges they face, and the system architecture, the SE process can develop an understanding of the “gaps” that exist and of the levels of risk they impose on a critical infrastructure system’s functional, physical and operational performance. Understanding this, essential use-appropriate mitigations can be identified, or if need be, developed, and a resilient, solution-agnostic PNT requirement document created.
The Way Forward
The Critical Infrastructure Resilience Institute (CIRI), a U.S. Department of Homeland Security Center of Excellence, notes that “critical infrastructure systems are facing a myriad of challenges. Solutions must address the cyber, physical and human dimensions.” They keyed into four areas where critical infrastructure resilience activities should be directed: building the business case, information policy and regulation, developing new tools and technologies, fostering and educating the workforce.
These include the recognition that “policy and regulation have a powerful impact on market forces.” While the fact that “most U.S. infrastructure is owned and operated by the private sector” is a challenge, it should not be an excuse.
We must start immediately to re-establish strong SE practices, policies, and principles to help critical users understand their needs and determine the metrics required to ensure safety and “preclude significant economic impact.” Only then can we understand from a national perspective, the needed safety and security metrics and what constitutes significant economic impact, and then establish categories of solution-agnostic requirements. Lacking these clear resilience targets, detailed planning, and required resource commitments, the growing threats of PNT vulnerability will continue only to be admired, rather than be mitigated. Hope is not a strategy, but this systems engineer hopes that it does not take a truly catastrophic event to finally prompt much needed and long overdue actions.
Mitch Narins is the principal consultant/owner of Strategic Synergies LLC, a consultancy he formed following more than 40 years of U.S. government service. He is a Fellow of the Royal Institute of Navigation, a aenior member of the Institute of Electrical and Electronic Engineers, a member of the Institute of Navigation and head of its Washington, D.C., section, and a member of RTCA, RTCM, IEEE and SAE Standards Committees.