No audio available for this content.
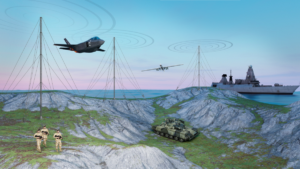
Tests of the robustness of commercial GNSS devices against threats show that different receivers behave differently in the presence of the same threat vectors. A risk-assessment framework for PNT systems can gauge real-world threat vectors, then the most appropriate and cost-effective mitigation can be selected.
Vulnerabilities of GNSS positioning, navigation and timing are a consequence of the signals’ very low received power. These vulnerabilities include RF interference, atmospheric effects, jamming and spoofing. All cases should be tested for all GNSS equipment, not solely those whose applications or cargoes might draw criminal or terrorist attention, because jamming or spoofing directed at another target can still affect any receiver in the vicinity.
GNSS Jamming. Potential severe disruptions can be encountered by critical infrastructure in many scenarios, highlighting the need to understand the behavior of multiple systems that rely on positioning, and/or timing aspects of GNSS systems, when subject to real-world GNSS threat vectors.
GNSS Spoofing. This can no longer be regarded as difficult to conduct or requiring a high degree of expertise and GNSS knowledge. In 2015, two engineers with no expertise in GNSS found it easy to construct a low-cost signal emulator using commercial off-the-shelf software–defined radio and RF transmission equipment, successfully spoofing a car’s built-in GPS receiver, two well-known brands of smartphone and a drone so that it would fly in a restricted area.
In December 2015 the Department of Homeland Security revealed that drug traffickers have been attempting to spoof (as well as jam) border drones. This demonstrates that GNSS spoofing is now accessible enough that it should begin to be considered seriously as a valid attack vector in any GNSS vulnerability risk assessment.
More recently, the release of the Pokémon Go game triggered a rapid development of spoofing techniques. This has led to spoofing at the application layer: jailbreaking the smartphone and installing an application designed to feed faked location information to other applications. It has also led to the use of spoofers at the RF level (record and playback or “meaconing”) and even the use of a programmed SDR to generate replica GPS signals — and all of this was accomplished in a matter of weeks.
GNSS Segment Errors. Whilst not common, GNSS segment errors can create severe problems for users. Events affecting GLONASS during April 2014 are well known: corrupted ephemeris information was uploaded to the satellite vehicles and caused problems to many worldwide GLONASS users for almost 12 hours. Recently GPS was affected. On January 26, 2016, a glitch in the GPS ground software led to the wrong UTC correction value being broadcast. This bug started to cause problems when satellite SVN23 was withdrawn from service. A number of GPS satellites, while declaring themselves “healthy,” broadcast a wrong UTC correction parameter.
Atmospheric Effects. Single frequency PNT systems generally compensate for the normal behavior of the ionosphere through the implementation of a model such as the Klobuchar Ionospheric Model.
Space weather disturbs the ionosphere to an extent where the model no longer works and large pseudorange errors, which can affect position and timing, are generated. This typically happens when a severe solar storm causes the Total Electron Count (TEC) to increase to significantly higher than normal levels.
Dual-frequency GNSS receivers can provide much higher levels of mitigation against solar weather effects. However, this is not always the case; during scintillation events dual frequency diversity is more likely to only partially mitigate the effects of scintillation.
Solar weather events occur on an 11-year cycle; the sun has just peaked at solar maximum, so we will find solar activity decreasing to a minimum during the next 5 years of the cycle. However that does not mean that the effects of solar weather on PNT systems should be ignored for the next few years where safety or critical infrastructure systems are involved.
TEST FRAMEWORK
Characterization of receiver performance, to specific segments within the real world, can save either development time and cost or prevent poor performance in real deployments. Figure 1 shows the concept of a robust PNT test framework that uses real-world threat vectors to test GNSS-dependent systems and devices.
We have deployed detectors — some on a permanent basis, some temporary — and have collected extensive information on real-world RFI that affects GNSS receivers, systems and applications.
For example, all of the detected interference waveforms in Figure 2 have potential to cause unexpected behavior of any receiver that was picking up the repeated signal. A spectrogram is included with the first detected waveform for reference as it is quite an unusual looking waveform, which is most likely to have originated from a badly tuned, cheap jammer. The events in the figure, captured at the same European sports event, are thought to have been caused by a GPS repeater or a deliberate jammer. A repeater could be being used to rebroadcast GPS signals inside an enclosure to allow testing of a GPS system located indoors where it does not have a view of the sky.
The greatest problem with GPS repeaters is that the signal can “spill” outside of the test location and interfere with another receiver. This could cause the receiver to report the static position of the repeater, rather than its true position. The problem is how to reliably and repeatedly assess the resilience of GPS equipment to these kinds of interference waveforms. The key to this is the design of test cases, or scenarios, that are able to extract benchmark information from equipment. To complement the benchmarking test scenarios, it is also advisable to set up application specific scenarios to assess the likely impact of interference in specific environmental settings and use cases.
TEST METHODOLOGY
A benchmarking scenario was set up in the laboratory using a simulator to generate L1 GPS signals against some generic interference waveforms with the objective of developing a candidate benchmark scenario that could form part of a standard methodology for the assessment of receiver performance when subject to interference.
Considering the requirements for a benchmark test, it was decided to implement a scenario where a GPS receiver tracking GPS L1 signals is moved slowly toward a fixed interference source as shown in Figure 3.
The simulation is first run for 60 seconds with the “vehicle” static, and the receiver is cold started at the same time to let the receiver initialise properly. The static position is 1000m south of where the jammer will be. At t = 60s the “vehicle” starts driving due north at 5 m/s. At the same time a jamming source is turned on, located at 0.00 N 0.00 E. The “vehicle” drives straight through the jamming source, and then continues 1000m north of 0.00N 0.00E, for a total distance covered of 2000m. This method is used for all tests except the interference type comparison where there is no initialization period, the vehicle starts moving north as the receiver is turned on.
The advantages of this simple and very repeatable scenario are that it shows how close a receiver could approach a fixed jammer without any ill effects, and measures the receiver’s recovery time after it has passed the interference source. We have anonymized the receivers used in the study, but they are representative user receivers that are in wide use today across a variety of applications. Isotropic antenna patterns were used for receivers and jammers in the test. The test system automatically models the power level changes as the vehicle moves relative to the jammer, based on a free-space path loss model.
RESULTS
Figure 4 shows a comparison of GPS receiver accuracy performance when subject to L1 CHIRP interference. This is representative of many PPD (personal protection device)-type jammers.
Figure 5 shows the relative performance of Receiver A when subject to different jammer types — in this case AM, coherent CW and swept CW.
Finally in Figure 6 the accuracy performance of Receiver A is tested to examine the change that a 10dB increase in signal power could make to the behavior of the receiver against jamming — a swept CW signal was used in this instance.
Discussion. In the first set of results (the comparison of receivers against L1 CHIRP interference), it is interesting to note that all receivers tested lost lock at a very similar distance away from this particular interference source but all exhibited different recovery performance.
The second test focused on the performance of Receiver A against various types of jammers — the aim of this experiment was to determine how much the receiver response against interference could be expected to vary with jammer type. It can be seen that for Receiver A there were marked differences in response to jammer type. Finally, the third test concentrated on determining how much a 10dB alteration in jammer power might change receiver responses. Receiver A was used again and a swept CW signal was used as the interferer. It can be seen that the increase of 10dB in the signal power does have the noticeable effect one would expect to see on the receiver response in this scenario with this receiver.
Having developed a benchmark test bed for the evaluation of GNSS interference on receiver behavior, there is a great deal of opportunity to conduct further experimental work to assess the behavior of GNSS receivers subject to interference. Examples of areas for further work include:
- Evaluation of other performance metrics important for assessing resilience to interference
- Automation of test scenarios used for benchmarking
- Evaluation of the effectiveness of different mitigation approaches, including improved antenna performance, RAIM, multi-frequency, multi-constellation
- Performance of systems that include GNSS plus augmentation systems such as intertial, SBAS, GBAS
CONCLUSIONS
A simple candidate benchmark test for assessing receiver accuracy when subjected to RF interference has been presented by the authors.
Different receivers perform quite differently when subjected to the same GNSS + RFI test conditions. Understanding how a receiver performs, and how this performance affects the PNT system or application performance, is an important element in system design and should be considered as part of a GNSS robustness risk assessment.
Other GNSS threats are also important to consider: solar weather, scintillation, spoofing and segment errors.
One of the biggest advantages of the automated test bench set-up used here is that it allows a system or device response to be tested against a wide range of of real world GNSS threats in a matter of hours, whereas previously it could have taken many weeks or months (or not even been possible) to test against such a wide range of threats.
Whilst there is (rightly) a lot of material in which the potential impacts of GNSS threat vectors are debated, it should also be remembered that there are many mitigation actions that can be taken today which enable protection against current and some predictable future scenarios.
Carrying out risk assessments including testing against the latest real-world threat baseline is the first vital step towards improving the security of GNSS dependent systems and devices.
ACKNOWLEDGMENTS
The authors would like to thank all of the staff at Spirent Communications, Nottingham Scientific Ltd and Qascom who have contributed to this paper. In particular, thanks are due to Kimon Voutsis and Joshua Stubbs from Spirent’s Professional Services team for their expert contributions to the interference benchmark tests.
MANUFACTURERS
The benchmarking scenario described here was set up in the laboratory using a Spirent GSS6700 GNSS simulator.