No audio available for this content.
By Logan Scott
Inexpensive, readily available GPS jammers constitute a threat to safety, national infrastructure, and industry revenue streams. Cell phones could incorporate GPS jam-to-noise (J/N) ratio detectors to provide timely interference detection and effective localization, with a flexible and updateable system since the crowd processing function resides in software.
Events in early 2010 at Newark Liberty International Airport demonstrate the vulnerability of civil GPS infrastructure to interference. Over a period of several weeks, sporadic outages of the GPS Ground Based Augmentation System (GBAS) located at the airport to provide precision approach services occurred, due to radio-frequency (RF) interference from unknown sources. Analysis showed that certain vehicles on a nearby freeway were the likely culprit(s), and an interdiction effort was launched to catch an offender. Using advanced interference detection equipment and multiple surveillance cameras, an offender — a truck driver — was caught and arrested. In his possession: a widely available $33 GPS jammer.
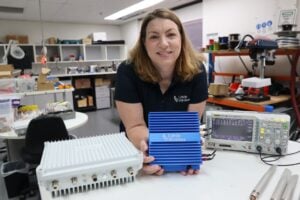
For sale over the Internet, the jammer emits 200 mW and plugs directly into a vehicle’s cigarette lighter (see photo). To prevent future incidents, the FAA is relocating the airport’s GBAS system to a more protected location away from the freeway.
Such an approach to jammer detection, localization, and enforcement, while successful in this instance, ultimately serves only as a stopgap. It took tremendous resources and several weeks to find one offender.
Increasing use of GPS jamming and spoofing to cover both licit and illicit activities is likely, given the general public’s desire for privacy and the general lack of awareness of how devastating GPS jamming can be. The $33 jammer in this instance could have affected critical flight operations 10 miles away. Currently, most jammers are not even detected; we simply have an unidentified GPS outage. It was only because of the technical sophistication of the FAA’s GBAS that the outage’s underlying cause was identified as jamming.

At the ION-GNSS 2010 plenary session, Phil Ward advanced the notion that cell phones could incorporate GPS jam-to-noise (J/N) ratio detectors to provide timely interference detection. Having an extensive background in cellular communications as well as GPS, I found the idea intriguing. In this article, I explore the viability of this concept, whether jammer location can be determined, and what it would take to implement such a system.
In urban and suburban areas, it appears feasible to provide warning of jamming in less than 10 seconds while providing real-time jammer location to better than 40 meters. Such a capability would aid immensely in mitigating jamming events by enabling effective law-enforcement action. Potential jammers will know they are likely to be caught and that the penalties are severe. They won’t do it after a few well publicized interdictions. The cost for this nationwide system can be relatively modest. It won’t take billions of dollars and decades to implement; it will take an act of national will similar to the phase II wireless E911 effort. IOC could happen as early as 2015, with full national coverage by 2017.
J911 System Architecture
Figure 1 depicts the automatic gain control (AGC, the process by which RF front-end gain is controlled so as to present the analog-to-digital (A/D) converter with appropriate signal levels) loop found in some form in virtually all GPS receivers. The core objective is to set the gain GA so a set percentage of 2-bit A/D converter outputs correspond to large values of 3 and -3. Typically, VT percentage is set to 35 percent in a Gaussian noise environment to hold A/D conversion losses to ~0.5 dB. In another popular variation, the 1.5 bit A/D converter, the zero threshold is not implemented and three possible values are output (-1, 0, and -1). Such a converter has about 0.9 dB of conversion loss if VT percentage is set to 40 percent, and considerably simplifies correlator processing.


Of particular interest for interference detection purposes, the control voltage to the AGC amplifier can also be used to measure jammer-to-noise power (J/N). Under unjammed onditions, the nominal input power to an L1 C/A receiver is about -110 dBm, most of this due to naturally occurring thermal and amplifier noise. The C/A code signal at -130 dBm is a factor of 100 weaker and does not influence AGC operation. If, however, interference starts rising above the thermal noise floor, the AGC will respond by decreasing gain GA so as to maintain the correct percentage in large outputs. Response times to a change in input power level are very fast, typically less than 1 millisecond, and so pulse jamming characteristics can be determined as well.
If the receiver knows the control characteristics of the AGC amplifier (β,α) then the receiver can determine the change in J/N given V1. Additionally, if the receiver knows the quiescent V1 associated with a thermal noise-only input, it can obtain J/N on an absolute scale. To obtain the quiescent value, the receiver can short the antenna on power-up as part of built-in test prior to operation. Alternatively, it can maintain and refine a historical value during normal operations, the caution being that spoofers and jammers may try to manipulate history-based values.
Even with relatively small jammers, front-end saturation can be a problem when the jammer is nearby. The thermal noise floor in a 1.7 MHz bandwidth is about -110 dBm, and so a J/N of 60 dB corresponds to jamming signal strength of -50 dBm. Accurate J/N measurements are possible at this level, but likely require adding a switchable input step attenuator in the down-conversion chain. Measuring J/N above this level gets problematic for a low-cost GPS front-end.
In a further refinement, receivers can include additional comparators set at -1.2 VB and + 1.2 VB. If a constant envelope (CE) jammer (CW, swept CW, or Gold code jammer types) is present, this threshold will be crossed 16 percent of the time given CE jamming, versus 32 percent of the time for Gaussian distributed jamming if VT percentage is set to 40 percent, as is typical for a 1.5 A/D converter. With the jammer type identified, the receiver can adapt V<su
b>T percentage if it is seeing CE jamming to obtain several dB of additional jamming resistance. The TI-420 L1 C/A receiver developed by my team at Texas Instruments in 1986 routinely outperformed P-code receivers against CE jammers using this technique. The takeaway from this discussion is that with very simple hardware, an L1 C/A receiver can measure J/N and also determine the approximate type of jamming that it sees: pulse, constant envelope, and Gaussian.
Can this information be used to detect and locate jammers? In Figure 2, a 200 mW jammer is located at the origin [0,0] and J/N (dB) is plotted as a function of relative location. Conceptually, phones located closer to the jamming source will see higher J/N than those further away. The aggregate of phones, each reporting J/N and own position, provides a basis for locating the jammer. Some phones may also report the type of jammer they are seeing. Information about phone type and its physical orientation would also be of use in interpreting and correcting raw J/N information with regards to antenna gain and accuracy.
Structurally, the J911 system would be very similar to the E911 system and would heavily leverage existing infrastructure and standards already in place. When a wireless E911 call is placed, the serving base-station(s) routes the call through a mobile switching center (MSC) where the call is identified as a 911 call. The MSC then connects the call to a local exchange carrier (LEC) who then connects the call to a public safety answering point (PSAP).
In the United States, 6,149 PSAPs are distributed around the country.Wireless E911 calls are connected to a specific PSAP usually based on the location of the caller as determined by the cellular carrier. Under Phase II requirements, E911 call takers receive both the caller’s wireless phone number and their location information. Currently, 95 percent of PSAPs have some Phase II E911 capability.
Using the E911 system as a basis, creating a federal J911 PSAP to process J/N measurements into jammer location estimates would not be all that problematic. Software upgrades to phones, base stations, MSCs, and so on, are routine and often include new or modified message provisions and capabilities. Adding a Jamming Report message type would use existing message transport and routing facilities already part of the infrastructure. The main infrastructure addition would be a facility to process jamming reports, either at the federal level or as an adjunct to existing PSAPs.
Adding a J/N measurement capability to phones is a straightforward hardware issue, but modifying extant phones is not feasible. Fortunately, cell phones typically have a two-year lifecycle before being replaced. Adding a jammer reporting capability can be accommodated through the normal replacement cycle.
J911 System Performance
Given the location and J/N measurements obtained by a crowd of randomly located cell phones, one approach to determining the jammer’s location is to perform a series of curve fits for a grid of hypothetical jammer locations and see which location provides the best fit. Figure 3 illustrates this process; for the moment, the cell phones (observers) are assumed to provide exact J/N and location measurements.
Here, a 200 mWatt jammer is located at xy = [0,0]. 1,000 cell phones are uniformly distributed over a surrounding 1-square-kilometer area. A hypothetical jammer location grid of points 5 meters apart is created over a span of ±150 meters in x and y. At each hypothetical point, the 250 highest non-saturated J/N reports are used in a least-squares curve fitting process that assumes jamming strength falls off as 1/Rα. (In the ground mobile environment, α is usually in the range of 2 to 4. α = 2 is consistent with a free space propagation model.)
Specifically, J/N (dB) is presumed to be a linear function of log10 (R) where R is the range from reported observer position to hypothetical jammer location. At each hypothetical jammer location point, the norm of the residuals is collected as a metric of how closely the jamming reports (J/N + location) matched the least squares curve fit. The smaller the norm of the residuals, the better the curve fit. This metric is plotted in Figure 3 and shows that the best fit is obtained at the true jammer location.

In practice, knowledge of cell-phone locations is imperfect, and for those phones near to the jammer, GPS will be unavailable. There are several alternatives for determining location. Cellular carriers use a plethora of location determination techniques based on round-trip timing between the cell phone and observing base stations. Another very good option is to use Wi-Fi-derived location based on visible access points (AP). Companies such as Skyhook and Google have commercialized this technology, and it is available now in most areas. Positioning accuracies of 30 meters are typical, absent GPS. Looking down the road a bit, many phones now have integral accelerometers and could in the future propagate position with good accuracy even when GPS is unavailable.
Another very important factor is that J/N observations are going to be highly variable.
Three major effects to consider:
- Cell phone errors in measuring J/N due to quiescent V1 errors, imperfect AGC amplifier characterization, and uncompensated receive antenna gain directionality.
- Variability in J/N due to large-scale shadowing due to buildings, hills, bridges, etc.
- Variability in J/N due to small-scale multipath effects. Jamming signals may follow multiple paths to the cell phone and add up constructively or destructively. Moving the cell phone a few inches may yield a very different J/N.
To model these effects, a log normal model of J/N measurement deviation from ideal free-space propagation is used. In this model, free-space propagation represents median signal strength and σ log normal, expressed in dB, describes Gaussian random deviation from the median signal strength. Such models are widely used in predicting statistical cellular coverage and have a strong correlation with real-world observations.
Figure 4 shows a jammer location metric manifold computed using the same process as in Figure 3, except now with observer location errors of
σx = σy = 30 meters and σ log normal = 6dB. Basically this says that the cell phones have Wi-Fi-based locations, and that the measured J/N is within ±6 dB of the free space value 68 percent of the time, and, within ±12 dB of the free-space value 95 percent of the time. These are relatively modest performance goals for the cell phones.

In this particular run, the hypothetical jammer position yielding smallest residual norm is at xyjammer = [10,45] meters. Even though the individual measurements are of poor quality, the crowd consensus yields a fairly accurate estimate of the jammer’s position.
Before continuing, a few words on crowd size and cell phone densities. Assuming a cellular penetration rate of 70 percent, Table 1 shows approximate cell-phone densities for select suburban and urban municipalities. No doubt there is considerable variation in cell phone densities even within a municipality, but as a rough order of magnitude, 1,000 cell phones per square kilometer is not an unreasonable number.

Figure 5 shows statistics of jammer location accuracies, presuming a uniformly distributed cell phone density of 1,000 cell phones per square kilometer. Based on a simulation of 500 independent runs, this figure plots jammer location radial error statistics assuming 25, 100, 500, or 1,000 measurements are processed in the curve-fitting process where radial error is given by:
Processing the full crowd yields 14-meter or better radial errors in 50 percent of the trials and better than 27 meters in 90 percent of the trials. So why process less than the full set of measurements obtained by the cell phones? In practice, if all cell phones observing a jamming event were to report everything they see, the cellular infrastructure could be overwhelmed. To limit traffic surges and to limit false alarms, a jamming event is likely to be processed in two distinct phases; the detection phase and the locating phase.

Jammer Detection
In the detection phase, cell phones would report relatively infrequently based on which page group they are in. In current practice, to minimize cell-phone power consumption while in standby, each cell phone belongs to a particular page group based on its supposedly unique International Mobile Equipment Identity or IMEI. (As a bit of trivia, most cell phones display their IMSE if you dial *#06#). In GSM there may be 50 distinct page groups. Depending on which page group the phone belongs to, the phone knows when to wake up to listen to the paging channel (PCH) and see if there is an incoming call for it. By limiting jammer reporting based on which page group the phone is a member of (or IMEI), the size of the initial traffic surge can be limited.
During the detection phase, the system will also need to determine the type of interference event being seen. A solar event may trigger large numbers of phones, but the flat J/N versus location response can be used to rule out a localized jamming event. A real jamming event will tend to have a geographic center with many high J/N values over a fairly restricted area. Also, if CE interference is reported as opposed to Gaussian interference, there is good confidence the event is human originated, and the source can be located.
Jammer Localization
If jamming is determined to be the cause of interference, then the system transitions to a jammer localization phase. Tentatively, the jammer location process would seem to be better served by using phones near the jammer, but not those phones with saturated J/N meters. The non-saturated phones provide good RSSI (received signal strength indicator) information that is correlatable with distance, and those cell phones closest to the jamming source (high J/N) tend to experience fewer propagation anomalies. To control traffic loads during a jamming event, the J911 PSAP may restrict which phones report by requesting that only phones seeing a J/N value of greater than J/Nmin report.
Returning to Figure 5, processing the full set of data yields better snapshot jammer location accuracy as opposed to results obtained using a trimmed subset. Processing the full crowd yields 14 meter or better radial errors in 50 percent of the trials and better than 27 meters in 90 percent of the trials. Relying on only the subset of the 250 strongest J/N values adversely affects jammer snapshot location accuracy; yielding 47 meter or better radial errors in 50 percent of the trials and better than 110 meters in 90 percent of the trials.
The upside is that the traffic generated on the cellular network is one quarter as much. Stated another way, for a given traffic handling capacity, we could update jammer location at four times the rate. Using page group membership, general location, or IMEI as an additional reporting criteria, we can sample different cell-phone populations at each snapshot interval.
If a Kalman filtering approach is used to track/smooth jammer location estimates, the reduced set of observations may ultimately yield better performance, especially considering that individual phones can move around considerably over time. Also, geographical centroiding using phones with saturated or very high J/N indications may be another viable jammer locating technique, and perhaps combining approaches would be good. If the jammer is determined to be in a vehicle, substantial accuracy improvements in location accuracy may also be obtained by limiting the hypothetical jammer location grid to include only roads based on map input. These are all open issues for further study.
Figure 6 repeats the analysis of figure 5 except now, cases of much reduced cell-phone density are considered. In all cases, the full set of data is reported and processed. Not surprisingly, with more observers, the jammer locating accuracy is better, but even with low cell-phone densities, the performance is not bad: 50 meters 50 percent of the time, and 100 meters 90 percent of the time with 100 phones per square kilometer. Jamming detection and location is feasible in modestly populated areas.

Figure 7 shows radial accuracy statistics for σlognormal = 4, 6, 8 and 10 dB. As expected, as J/N measurement reliability deteriorates due to increased propagation variability and/or cell phone measurement errors, the accuracy of jammer location estimates also deteriorates but not catastrophically so.

Similarly, simulation runs with larger cell-phone location errors showed modest performance losses in jammer location accuracy. In aggregate, Figures 5 through 7 point towards crowd size and crowd selection algorithm, not the accuracies of individual measurements, as the main driving factors in jammer-location accuracy.
Putting J911 in Place
Initially, wireless operators had little enthusiasm for implementing wireless E911 as it introduced substantial hardware requirements for mobile station (MS) position reporting (a cell phone is an MS). Now, E911 provides the technical underpinning for numerous revenue streams, most notably the location-based services (LBS) industry. GPS jamming is a direct threat to this revenue stream.
As GPS becomes integrated with vehicle navigation systems and intelligent highway systems, cellular carriers will play an important role in provisioning needed communications facilities. GPS jamming is a direct threat to this future revenue stream.
Cellular signal jamming is also a threat to national infrastructure (and carrier revenue). The approaches described above are readily adaptable to detecting and locating cellular frequency band interference sources in a timely manner. By emphasizing the potential benefits of a J911 system to the cellular carriers, there is better potential for buy-in by industry.
Using the wireless E911 experience as a model, J911 could be made a reality using a three-step process:
Rulemaking. After validating the requirement, the FCC would issue a Notice of Proposed Rulemaking (NPRM) stating the system functional requirements. Industry would comment, and through an iterative process the J911 requirements regarding performance and mandated deployment schedules would be established. This process would take about two years.
Standards Setting. Well established wireless, LEC, and PSAP standard-setting bodies would create detailed standards for implementing J911. The bulk of the work would be done by collaborating representatives from industry. Standards would be issued for various system portions — for example, MS standards, BSS standards, and so on — to permit manufacturers to build interoperable equipment. The standards setting process would take one to two years.
Rollout. With the exception of the MS portions, J911 does not require hardware modifications to the cellular infrastructure. J911 would be implemented and deployed as part of the normal update and release cycle. Under the mandate, new mobile stations would have to meet the requirements of the FCC rulemaking and standards setting processes. Over a two-year period, mobiles would transition to J911 capable models and the J911 system would be in place.
Crowdsourcing
In the March 7, 1907, issue of Nature, Francis Galton reports on an experiment where, at a county fair, he had 787 people guess the dressed weight of a fatted ox, charging them six-penny a guess. Individual estimates varied wildly, as did the expertise of the guessers. However, the median estimate of the crowd was within 0.8 percent of the correct value.
Conclusions
Creating a national infrastructure for detecting and locating GPS and cellular jammers is needed. Such a capability would provide the underpinnings for rapid and effective enforcement actions. Crowdsourcing approaches using a multitude of opportunistic cell phone based observers appears a plausible solution providing timely and location specific alerts. Even though the individual measurements are of poor accuracy, the crowd consensus yields good accuracy. While this system would not reliably detect purpose-built precision power-controlled spoofers, it could detect coarser cell-phone apps-style spoofers that might, for example, be seen in road-use tax avoidance.
Numerous open issues remain. Jammer antenna gain patterns can adversely affect locating accuracy. To what extent can this be mitigated by mapping out antenna gain contours? How can multiple simultaneous jammers be resolved? Can map and propagation modeling based aiding algorithms improve jammer location accuracy?
Significant research is needed, but the proposed system is open for continual improvement, even after it is fielded, since the crowd processing function resides in software.
Logan Scott is a consultant specializing in radio frequency signal processing and waveform design for communications, navigation, radar, and emitter location. He has more than 32 years of military and civil GPS systems engineering experience. As a senior member of the technical staff at Texas Instruments, he pioneered approaches for building high-performance, jamming-resistant digital receivers. He is currently active in location-based encryption and authentication, high performance/low bias adaptive array technologies, and RFID applications. He teaches Navtech Seminars’ New Signals course and holds 32 U.S. patents.