No audio available for this content.
We’ve heard a lot in the news recently about GPS spoofing, mostly centred on the story of ship spoofing in the Black Sea. Between June 22-24, a number of ships in the Black Sea reported anomalies with their GPS-derived position, and found themselves apparently located at an airport.
What happened is open to educated conjecture. In this column, I’ll briefly cover the history of spoofing, its basic techniques, some spoofing tests that we conducted, and then return to the infamous Black Sea incident.
As part of my day-to-day work in navigation warfare, I do a fair amount of work in defensive anti-spoofing. Naturally, in order to test anti-spoof technology, it is necessary to also perform spoofing. It’s a delicate subject and, as with any topic involving defense or national security or critical infrastructure, there’s a balance to strike between responsible disclosure, how much information is released into the public domain, and so on.
In this article, I will stick firmly to information available in the public domain, lest I be accused of proliferating the threat, but this still gives us enough material to tiptoe around the subject for the benefit of our readers. I could have included more details about the spoofing attacks, but was advised to hold some back — it makes governments nervous. You can read some of the background in an excellent article by Norwegian broadcaster NRK and a Resilient Navigation and Timing Foundation press release. Similar GPS anomalies still continue to occur at various locations.
Let’s start with basic spoofing background, and we’ll return to the Black Sea incident at the end of the article.
A brief history of spoofing
Spoofing isn’t a new threat — it’s been around for decades. But only in recent years has it received so much public attention. As with jamming and anti-jamming technology, and most other topics in the GPS domain, spoofing finds its roots back in the days of Cold War radar. In those times, it was often known as “deception jamming,” where you would transmit fake radar returns to paint an incorrect picture on your adversary’s radar screen.
When GPS came along, it was understood at the time that the C/A code would be vulnerable to spoofing. It’s an open code, so anyone is free to reproduce it. That is, after all, what a GPS simulator is: a GPS spoofer. We legitimately test our GPS receivers by fooling them with fake signals from a GPS simulator.
Of course, this is precisely why legacy GPS satellites also transmit the military P(Y)-code, and continue to do so. The P-code offers improved accuracy, and some other benefits, but more importantly, it is modulated with the W encryption sequence to give us the encrypted P(Y)-code. Ever since the anti-spoofing module was set to the “on” state, unless you have the key, you are unable to directly spoof the P(Y)-code. (You can still perform a meaconing attack, though, where you simply record the transmitted satellite signals and retransmit them again. Although this kind of attack can’t be used to impose a particular scenario on a GPS receiver, it might still cause havoc in unwary receivers).
So. in the early days it can be argued that the spoofing threat was solved. It wasn’t until GPS became ubiquitous in the commercial and civilian domain that spoofing really raised its head again. The fact that the vast majority of GPS receivers in the world relied solely on the unencrypted C/A code became a cause for concern — especially where those GPS receivers were essential to critical infrastructure.
The threat of GPS spoofing was discussed at many conferences and behind many closed doors and, although most people agreed that spoofing was a theoretical threat, some people argued that in reality it was “simply too hard” to conduct a realistic spoofing attack. And therefore we should not worry ourselves about it.
It wasn’t until a couple of high-profile demonstrations were carried out by the University of Texas Radionavigation Laboratory that spoofing became front-page news once again. In 2012, the lab staff carried out an exercise at White Sands Missile Range where a GPS-guided drone was spoofed from a distance. The drone was fooled into thinking its altitude was increasing, causing it to compensate by dropping straight down. Then in 2013, the same team demonstrated how an $80 million yacht could be steered off course by means of a spoofing attack.
These exercises publicly demonstrated that spoofing was indeed a real threat, and could be done. But many people still believed that it was very hard to build the complex equipment necessary to perform the attack, and thus spoofing was out of reach for most potential criminals or terrorists.
Fast forward another two or three years, to when a new mobile phone game appeared. Pokemon GO became the game craze of the moment, where players would travel around the country with their phones, getting points by collecting creatures in an augmented reality world. It didn’t take long for people to dream up new ways of earning points in the game, without having to go to the effort of traveling around the world.
What if you could make your phone think it was somewhere else, without ever having to leave your bedroom? And thus, bizarrely, it was a mobile phone game that brought GPS spoofing into the mainstream.
The rise of the low-cost software-defined radio (SDR) has enabled “spoofing for everyone.” Today, the tool of choice for the casual user is often the HackRF or bladeRF. Couple small SDRs that cost around $200 with open-source GPS simulation software, and you have a basic spoofer. Plenty of websites detail how to perform basic spoofing, and at hacker gatherings, people can present how they spoofed a drone. These may not be the most sophisticated setups, but it’s good enough to do the job in many cases. With a better setup, which I won’t describe here, it’s possible to achieve a much more realistic attack, which will fool even the most shrewd and wary GPS receivers.
Spoofing basics
Let’s take a quick look at what it means to spoof GPS. A receiver searches for a satellite over a two-dimensional surface to find a correlation peak, and it must examine a range of Doppler frequencies and code offsets. An example is shown in Figure 1. Once the receiver finds the peak, the satellite is acquired, and it will then track the satellite as it moves and can demodulate the navigation data message.
When a spoofer comes along, it tries to recreate this peak. By doing so, and usually with little more power than the real satellites, the receiver will begin to track the spoofed signal. Once the spoofed signal is being tracked, the spoofer can begin to manipulate reality by slowly modifying the properties of the signal.

A poor spoofer doesn’t always align itself very well with reality, which essentially creates a second peak on the correlation surface. But a gullible receiver can still be fooled by this, and may lock on to false peaks.
The reality of spoofing and anti-spoofing
To understand the reality of spoofing and anti-spoofing, we carried out outdoor experiments at one of the Roke Manor trials areas (thanks go to my colleague Mike Wells for letting me use some of his results here).
In the first experiment (Figure 2), we spoof a commercially available mass-market receiver. The receiver is outside, reporting its correct location at Roke Manor. When we commence the spoofing attack, we are able to take control of the receiver. Once captured, we can then make the receiver appear to follow an arbitrary course. Here we make it wander off into the forest, spelling the word “roke” as it goes.

In the next experiment (Figure 3), we place a conventional anti-jam antenna (a CRPA) on the receiver. What we observe, as you might expect, is that the basic CRPA offers no protection against the spoofing attack.

Now let’s make the experiment more interesting. We’ll move away from the basic commercial receiver, and replace it with a unit that contains not only a GPS receiver, but also a 3-axis accelerometer, 3-axis gyro, 3-axis magnetometer and a barometric sensor. An Extended Kalman Filter (EKF) performs an optimal fusion of the various sensors to yield the position solution.
The result, when we again try our spoofing attack, is shown in Figure 4. In short, the receiver is still successfully spoofed, despite the additional sensor inputs it offers.

Before everyone gets too depressed by the ease at which GNSS, and even GNSS fused with other sensors, can be spoofed, there are answers to this problem. Some decent, modern GNSS receivers contain a whole host of algorithms for detecting and ignoring spoof signals. The issue is that many legacy receivers are still in the field, and these can be extremely vulnerable indeed.
Another option is to use a more advanced CRPA, which offers anti-spoof capabilities. These adaptive antennas are able to correlate on the spoof signals, and then remove them based on direction of arrival. So, in our final experiment here, we use our commercial mass-market receiver again, and protect it with an anti-spoofing CRPA.
The result is shown in Figure 5. You can see that the receiver is briefly spoofed, and starts to wander off course. When the anti-spoof is enabled and kicks in, the position quickly drifts back to the true location and stays there. Good job.

Back to the Black Sea
Let’s finish by returning to the hot topic of the day. Did spoofing occur in the Black Sea back in June? Or was it a different form of interference? Could it have been a low-level jamming incident, causing the GPS receivers to report misleading information?
Without resorting to SIGINT (signals intelligence) data, and basing this discussion solely on public domain information and anecdotal evidence, I would say this was almost certainly a spoofing incident. A number of factors lead to this conclusion, and I’ll share some of them.
- Firstly, it didn’t happen to one ship – it happened to over 20 separate vessels. So it wasn’t a malfunctioning GPS unit; it was an external incident of some kind.
- Secondly, a large number of ships in the area reported identical or very close locations. This is a symptom of a large-scale spoofing attack. If it was a low-level jamming attack, then any misleading positions reported by vessels would typically have some randomness to them.
- Thirdly, ships reported that their positions would periodically “jump” from the true location to the incorrect location. Again, this is very typical behavior in some spoofing experiments: For various reasons, GPS receivers may temporarily lose lock on a spoof set of satellites, and then reacquire the real ones, and vice versa. This causes the characteristic random flipping between two well-defined locations.
If we accept that a GPS spoofing attack did occur, it brings us to the million-dollar question.
Who did the spoofing, and why?
What I’ll do here is a bit of a lightweight analysis exercise using public information and basic physics, and you can formulate your own conclusions.
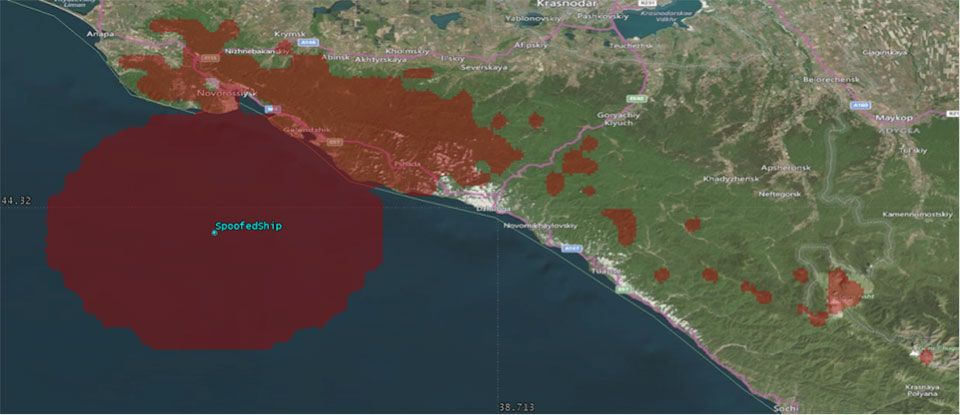
Let’s start by placing a ship, located in the Black Sea at 44°14.0’N 037°43.1E, which is the actual position of one of the reported spoofed vessels. For this example, I have placed a representative GPS antenna on the ship’s mast, with its antenna pattern shown.

To get a rough handle on the scenario, consider the possible propagation of the spoofing signal. As a first-order approximation, let’s assume a standard 4/3 Earth refraction model, with obstruction by terrain. That’s a reasonable assumption at this frequency: Any obscuration by terrain will block the spoof signal. Let’s also initially assume that our GPS antenna on the ship is mounted 38 meters above sea level, and our spoofing equipment is mounted on a mast 20 meters aboveground. From this information, we can plot a map of possible spoofer locations for this particular incident (Figure 7).

The first thing we might conclude from this is that the spoofing indeed originates from Russian territory, close to the Black Sea coast. To spoof the ship from further afield would require a much higher antenna, or even an airborne antenna. Which, of course, is possible, but then we would also expect vessels over a much wider area to report interference.
To me, it’s fairly conclusive that spoof GPS signals are being transmitted from this area, to make GPS receivers in the area think they are at an airport. The final question is: “Why would someone do this?” To answer this question, we must resort to educated speculation. Why would you want to spoof GPS receivers into thinking they are at an airport?
There’s one explanation that fits very nicely: drone defense. Many drones, especially those operated by casual users, have geofencing rules that prevent flights over airports and other restricted areas. So, if you were trying to perform aerial surveillance of the Russian border, your drone may suddenly think it was over an airport, and take action accordingly. The action taken depends, of course, on how the drone is programmed, but often includes “land immediately” or “return to launch point.” Certainly some of the drones we operate will immediately attempt to land if they find themselves in restricted airspace.
So if your drones are falling into the sea, you now have one idea why.