No audio available for this content.
Spirent Communications, a testing navigation and positioning systems company, today announced the introduction of Spirent SimSAFE, a software solution that concurrently simulates legitimate Global Navigation Satellite System (GNSS) constellations and spoofed or hoax signals to evaluate receiver resilience and help develop counter measures. SimSAFE was developed in conjunction with Qascom, GNSS signal security and authentication experts.
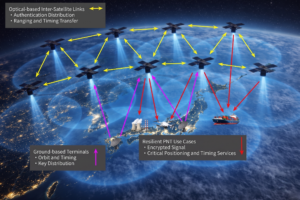
As GNSS become increasingly embedded in modern infrastructure for application timing and device positioning, the opportunities for interference and spoofing attacks become greater, Spirent said. Hoax or spoofing attacks work by mimicking genuine GNSS signals, which mislead GNSS receivers. From mobile telephony to Internet banking, GNSS timing signals are used in many key systems, and yet there is no requirement on GNSS equipment to demonstrate any degree of robustness to block or even detect malicious attacks that disrupt performance. Often, affected receivers do not recognize when they are receiving fake signals and continue to operate normally, but provide false time or position information.
“GNSS signal vulnerability is becoming a significant issue,” said John Pottle, marketing director of Spirent’s Positioning Division. “SimSAFE is the first tool to help develop systems that will detect and counter spoofing attacks. This solution is unique in being able to provide a means of both emulating a spoof attack and monitoring a receiver under attack to evaluate mitigation strategies and countermeasures.”
SimSAFE is a fully controllable laboratory-based, non-radiated test solution to evaluate a receiver’s response to a wide range of spoofing attacks. The test tool generates simulated spoofing attacks that can be aligned with genuine signals from an antenna or locally generated “genuine” signals using a Spirent GNSS simulator. This allows users to simulate a wide range of sophisticated attacks, monitor the response of the receiver under attack and evaluate the effectiveness of proposed countermeasures to then improve resilience against such attacks.

In essence Spirent’s SimSAFE spoofing test bed does two things:
- Generates simulated spoofing attacks where a Spirent RFCS is controlled to represent a hoax signal synchronized with a “genuine” signal which can be ambient GNSS or itself generated by simulation.
- Monitors a GNSS receiver subject to simulated spoofing attack in order to evaluate and refine mitigation strategies or countermeasures.
The two principal applications of SimSAFE are:
- The evaluation of the vulnerability of a user’s receiver when exposed to a wide range of simulated spoofing attacks.
- The evaluation and refinement of spoofing mitigation techniques, signal authentication strategies or countermeasures. This work can be conducted using any receiver of the user’s choice; however, a range of receiver monitoring tools supplied with SimSAFE are enabled if the receiver supports Septentrio Binary File (SBF). A suitable Septentrio receiver is supplied in the standard configurations for this purpose.