No audio available for this content.

GNSS Receiver Fingerprinting for Security-Enhanced Applications
By Daniele Borio, Ciro Gioia, Gianmarco Baldini and Joaquim Fortuny, European Commission, Joint Research Centre (JRC), Directorate E: Space, Security & Migration. Presented at ION GNSS+, September 2016.
GNSS data faking is similar to node forgery in a wireless network: A simulator or another device can be used to impersonate an actual GNSS receiver in a system which uses GNSS services. In this way, misleading Position, Velocity and Time (PVT) information can be send to the final PVT user in the system. To mitigate the risk of GNSS data faking, GNSS receiver fingerprinting can be adopted in security-enhanced applications to verify, at least to a certain extent, the authenticity of GNSS data.
For example, the injection of GNSS fake data in an Intelligent Transport Systems (ITS) vehicle platform could be identified using GNSS receiver fingerprinting.
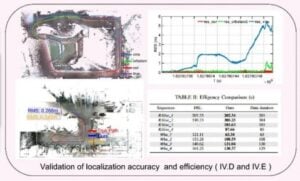
This paper investigates the potential of receiver clock bias and drift as sources of features for fingerprinting. In particular, several features, including Allan Deviation (ADEV), maximum and Root Mean Square (RMS) Time Interval Error (TIE) and correlation of the clock time series, have been investigated. The potential of the different features has been empirically investigated. It shows that three features are sufficient to discriminate the different receiver types. In particular, the ADEV and the Maximum TIE (MTIE) at 1 second, and the correlation value at 20 seconds have been selected for fingerprinting. These features allow one to effectively cluster the different receiver types and to build a “white list” for receiver identification.