No audio available for this content.

Logan Scott, principal at LS Consulting, is the inventor of an asymmetric navigation security paradigm for civil GPS signals that avoids the need for secure key storage in civil receivers and allows for widespread adoption in applications without physical security capabilities. Scott received the 2018 Signals Leadership Award from GPS World magazine. Read his acceptance speech below.
A crucial first step in developing resilient responses is to recognize that there is a problem so you can isolate it. Otherwise, an overly trusted element can contaminate the solution.
I am honored to accept this award from GPS World and our sponsors tonight. It has been a long journey from my initial vision of how civil signals might be authenticated to where we are now, with a draft Chimera signal specification nearing readiness for review.
I’d like to thank the Air Force Research Laboratory for sponsoring these efforts, and I would also like to acknowledge the outstanding efforts of the entire signals working group without whom this milestone would not have been reached: Captain Katie Carroll, Jon Anderson, Joanna Hinks and Nate DeVilbiss who brought me in on the project; Joe Rushanan and Jim Gillis who taught me so much about cryptography; Renee Yazdi and Brady O’Hanlon who pushed for no compromises. Working with this team has been one of the highlights of my professional career.
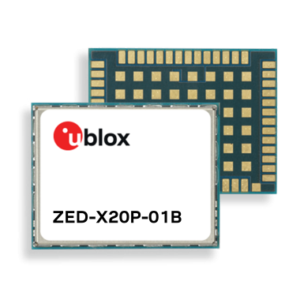
We have a solid design that fully realizes the benefits of chip-level binding with both fast and slow authentication capabilities. Chimera can offer security benefits far beyond the security theater of data message signing only. Moreover, it is a first step towards proving location.
Moving forward, the challenge I offer to you all is this: how can we establish the integrity and truthfulness of position and time reports both locally and remotely? How can we prove location, not only to ourselves but also to remotely located entities? In a world of autonomous vehicles, geofenced capabilities and information access, and an insecure supply chain, it is not enough to say that “I saw it on the C/A code.”
Complementary and overlapping techniques are essential in establishing the veracity of any claims. In support of this, we can and must provide assured spectrum protections for all GNSS systems.
Again, thank you very much for this award.