No audio available for this content.
Analysis of Satellite Data Exposes Threats to Civil Aviation
The Russian Federation is growing and actively nurturing a comparative advantage in the targeted use and development of GNSS spoofing capabilities to achieve tactical and strategic objectives at home and abroad.

A new report titled “Above Us Only Stars: Exposing GPS Spoofing in Russia and Syria,” presents findings from a year-long investigation ending in November 2018 on an emerging subset of electronic warfare (EW) activity: the ability to mimic, or spoof, legitimate GNSS signals to manipulate PNT data.
Using publicly available data and commercial technologies, the authors detect and analyze patterns of GNSS spoofing in the Russian Federation, Crimea and Syria. They profile different use cases of current Russian state activity to trace the activity back to basing locations and systems in use.
The report is issued by C4ADS, a Washington, D.C.-based nonprofit organization dedicated to providing data-driven analysis and evidence-based reporting on global conflict and transnational security issues. Its website, c4ads.org, lists transnational organized crime, proliferation networks (rogue nations and non-state actors), threat finance and supply-chain security as areas of focus.
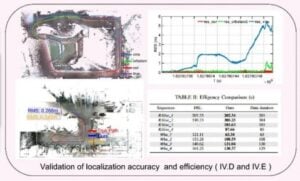
Pinpointing interference. Todd Humphreys, a University of Texas at Austin associate professor and head of the university’s Radionavigation Laboratory, collaborated on the research underpinning the report.
Humphreys stated that, as far as he knew, the study constitutes the first characterization of GNSS interference from space, and cited “some interesting findings:
“Using Automatic Identification System (AIS) data captured by overhead satellites, we monitored spoofing in the Black Sea, around St. Petersburg, Archangelsk, etc., and built a picture of interference activity that spans two years. All such activities occur near Russian coastal waters.
“Correlating this activity with the travel schedule of the Russian head of state, we have strong evidence that the spoofing is a protective measure used to thwart drone attacks on Vladimir Putin.
“By exploiting a software-defined GNSS receiver my lab is operating on the International Space Station, we were able to pinpoint a powerful source of interference, which we found to be coming from the northwest quadrant of a Russian-operated airbase in Syria. This explains the many reports of GNSS interference in the eastern Mediterranean during the past year.”
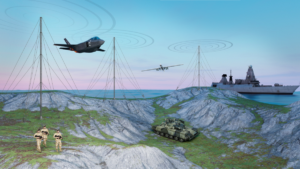
Global Threat. The tools and methodologies for perpetrating GNSS interference are proliferating at a rapid rate, and the frequency of such incidents around the world increases steadily. GNSS attacks, and GPS attacks specifically, now constitute an active, present, disruptive strategic threat in every theater of operation.
The C4ADS website, in announcing the report, states that “The Russian Federation has a comparative advantage in the targeted use and development of GNSS spoofing capabilities. However, the low cost, commercial availability and ease of deployment of these technologies will empower not only states, but also insurgents, terrorists and criminals in a wide range of destabilizing state-sponsored and non-state illicit networks. GNSS spoofing activities endanger everything from global navigational safety to civilian finance, logistics and communication systems.”
Examining GNSS spoofing events across the entire Russian Federation, its occupied territories and overseas military facilities, the report identifies 9,883 suspected instances across 10 locations that affected 1,311 civilian vessel navigation systems since February 2016. It demonstrates that these activities are much larger in scope, more diverse in geography, and longer in duration than any public reporting suggests to date.
C4ADS believes the Russian Federal Protective Service (FSO) operates mobile systems to support this activity. It chronicles the use of GPS spoofing in active Russian combat zones, particularly Syria, for airspace-denial purposes. This capability is scarcely reported in the public domain. C4ADS identified ongoing activity that poses significant threats to civilian airline GPS systems in the region.
The 66-page interactive report can be viewed at www.c4reports.org/aboveusonlystars, or downloaded as a PDF.