No audio available for this content.
Large coordinated cyber attacks from North Korea near its border with South Korea produced electronic jamming signals that affected GPS navigation for passenger aircraft, ships, and in-car navigation for roughly a week in late April and early May. To date, no accidents, casualties, or fatalities have been attributed to jammed navigation signals aboard 337 commercial flights in and out of South Korean international airports, on 122 ships, including a passenger liner carrying 287 people and a petroleum tanker. One South Korean driver tweeted “It also affects the car navigation GPS units. I am getting a lot of errors while driving in Seoul.”
South Korea experienced similar electronic attacks in March 2011, and in August and December of 2010, all of which were blamed on the North. The South Korean Defense Ministry said it is developing anti-jam programs to counter the attacks, which are being launched by what it termed a regiment-sized electronic warfare unit near the North Korean capital Pyongyang, and battalion-sized units closer to the inter-Korean border.
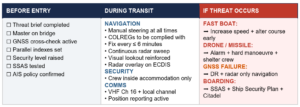
“Despite disruption in GPS, there is no serious threat to the safety of flights because planes are using other navigation devices,” claimed a Transport Ministry spokesperson. Officials say planes can use other navigation devices like very-high-frequency omni-directional range (VOR) and inertial navigation systems.
“We have traced the jamming signals to the direction of Kaesong,” said a Korean Communications Commission deputy director. Kaesong lies roughly 10 kilometers from the border between the two countries, and roughly 50 kilometers from downtown Seoul, Incheon International Airport, and the Yellow Sea.
It is unknown how long the jamming may continue, or when it might resume if halted. In March 2011, GPS jamming signals from the North lasted for 10 days during an annual U.S.-South Korea joint military drill. The motivation for North Korea to develop and employ anti-GPS technology would appear to come from its fear of attack by GPS-guided cruise missiles that might target key sites within the country. Clearly, any such military capability would require regular testing.
China is well known as a source of mass-produced small GPS jammers widely available over the Internet, but equipment on this scale would not be capable of jamming at the distances stated above. “At least one, or possibly more Russian companies are selling fairly powerful GPS jamming equipment,” said one knowledgeable source.
The source also alluded to Iran’s reported use of GPS spoofing to mislead and capture a U.S. surveillance unmanned aerial vehicle (UAV). Such an effort would similarly require large and sophisticated equipment, for which the most likely source is Russia.
“Receivers which cannot tolerate LightSquared will get in trouble in North Korea!” commented one well-known GPS manufacturer. “Today’s receivers don’t have protection. We just completed our ad [for the June issue of GPS World] which somewhat covers this.”
Other sources pointed to much wider potential threats than those in the Korean peninsula or areas of strategic conflict such as Afghanistan-Iran. Local jamming attacks can be anticipated almost anywhere, anytime: harassment by insurgent groups against established governments or armed forces, or GPS-denial actions by pirates in high-density commercial shipping lanes.
Since aviation is increasingly and in some cases exclusively dependent on GPS and regional GNSS augmentations or equivalents, jamming represents a growing concern for the aviation industry, including commercial airlines. In March of this year, the U.S. Federal Aviation Administration published an updated report on “Concept of Operations for NextGen alternative positioning, navigation and timing (APNT).” It advocates GPS backup by transponder-based distance-measuring equipment (DME), supported by onboard inertial reference systems, and assisted in places by low-powered GPS-like pseudolites and wide-area multilateration. The report concludes that any GPS/GNSS backup must be multi-modal, unjammable, provide GPS-like timing, have signals extending from the ground up to all altitudes, be unaffected by line-of-sight restrictions and, preferably, have reasonably long range to keep down the number of transmitting stations required.
Commenters have pointed out that eLoran meets those requirements, except for a vertical component, limiting it non-precision approaches. The system currently does not operate in the United States, although it is undergoing limited testing. The United Kingdom has a more active program. See upcoming GPS World webinar, Alternative PNT – Backing Up Critical Infrastructure with eLoran, on May 17.